Is it possible to connect AI to my databases and APIs securely?

Is it Possible to Connect AI to My Databases and APIs Securely?
As artificial intelligence (AI) increasingly integrates into business workflows and consumer technologies, a pressing question arises: can AI systems be connected securely to databases and APIs? The simple answer is yes, but achieving this requires a comprehensive approach to data security, access control, and system architecture. In this post, we’ll dive deep into the technical and strategic measures necessary to ensure that AI-driven applications operate securely with sensitive backend resources.
Understanding the Challenge: Why Connection Security Matters
AI models often require real-time or batch access to databases and APIs to make informed decisions. This might include retrieving customer data, inventory levels, or external market information. Any security breach involving these connections can lead to data leakage, unauthorized manipulation, or systemic failures.
“The power of AI is unlocked only when it can access rich, accurate data safely — without compromising privacy or security.”
Therefore, when integrating AI systems with databases and APIs, special attention must be given to:
- Authenticating and authorizing AI applications
- Encrypting data in transit and at rest
- Monitoring and logging data access
- Mitigating injection and man-in-the-middle attacks
Key Technologies and Best Practices for Secure AI Integration
1. Strong Authentication and Authorization
AI applications should never have unfettered access to databases or APIs. Instead, they must use secure API keys, OAuth tokens, or certificate-based authentication to verify identity. Role-based access control (RBAC) ensures that the AI can only perform permitted actions.
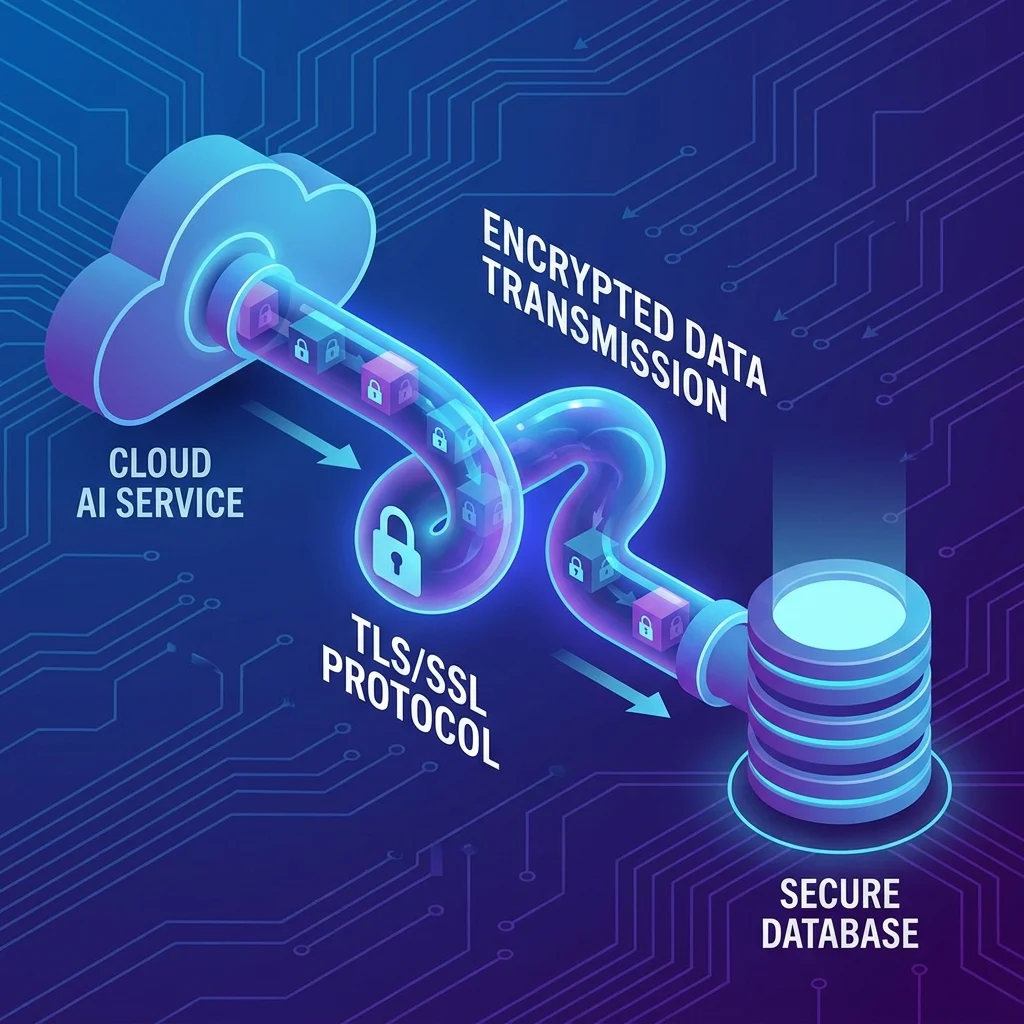
2. Transport Layer Security (TLS)
Encrypting data streams using TLS is essential to prevent eavesdropping or tampering during communication between AI services and data sources.
3. Data Encryption at Rest
In addition to encrypting data in transit, databases should encrypt sensitive information on disk, minimizing risk if storage systems are compromised.
4. Use of API Gateways
API gateways act as intermediaries, controlling, throttling, and sanitizing data requests from AI modules. They can also provide additional security layers like IP whitelisting and anomaly detection.
5. Secure Development Lifecycle
AI developers must follow secure coding standards to prevent injection flaws or exposure of secrets within source code. Security training and automated vulnerability scans contribute to this goal.
6. Audit Logging and Monitoring
Keeping detailed logs of AI interactions with databases and APIs helps detect suspicious activity and provides forensic data in case of breaches.
Architectural Patterns to Facilitate Secure AI Connections
Isolated Environments and Network Segmentation
Deploy AI systems within segregated environments that have limited and monitored network paths to backend systems. For example, use Virtual Private Clouds (VPCs) or subnetworks that restrict unauthorized access.
Federated Learning and On-Premises AI
Whenever possible, keep sensitive data within secure boundaries and train AI models locally, sending only aggregated or anonymized results externally. This approach reduces the need for direct access to data stores from public AI services.
Common Security Pitfalls to Avoid
- Hardcoding credentials: Embedding passwords or tokens in code or configuration files exposes secret keys.
- Overprivileged access: Granting AI services excessive permissions creates risks in case of compromise.
- Ignoring API versioning and patches: Using outdated APIs can expose vulnerabilities.
- Insufficient validation: Failure to sanitize inputs can lead to injection attacks.

Emerging Solutions and Tools
Several cloud providers and third-party vendors offer tools specifically designed to secure AI data connectivity:
- Secrets Management Services: Tools like AWS Secrets Manager, HashiCorp Vault, and Azure Key Vault store and rotate API keys and credentials securely.
- AI-Specific Firewalls and Monitoring: Some platforms provide anomaly detection focused on AI traffic patterns to identify potential misuse quickly.
- Privacy-Preserving AI Frameworks: Technologies like differential privacy and homomorphic encryption allow AI to learn from data without directly exposing sensitive details.
Conclusion
Connecting AI to your databases and APIs securely is not only possible—it’s essential for safeguarding your data assets and maintaining trust with your users and partners. By leveraging robust authentication, encryption, network segmentation, and continuous monitoring, organizations can empower AI-driven innovation while minimizing security risks.
Ultimately, security is an ongoing process requiring collaboration between AI developers, IT security teams, and infrastructure specialists. Investing in a comprehensive security strategy ensures that your AI integrations remain both powerful and safe.